Hardware-Rooted Video Authentication
Every signature is cryptographically signed. Every clip is verifiable. Every fake is exposed.
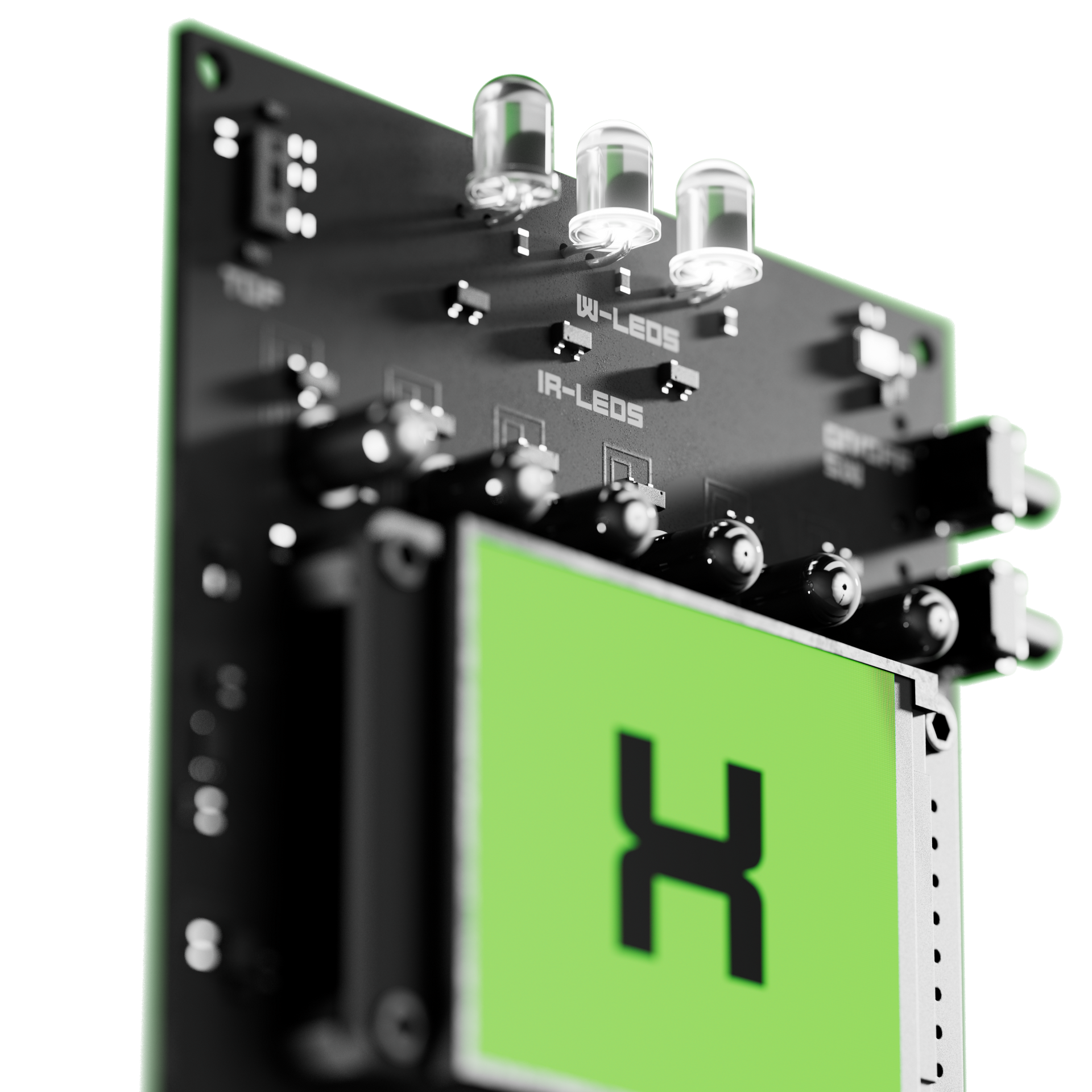
The Hardware Signal
Our device emits three simultaneous authenticity markers:
Together, these form a multi-layered optical + cryptographic fingerprint impossible to forge or replicate.
During Recording
Any camera captures the authenticity markers automatically.
No integration. No pairing. No software required.
If the device is in frame, the signals are recorded.
After Recording
Upload the clip to the verification portal.
The system performs the checkpoints.
If all checkpoints pass → Authentic.
If any checkpoint fails → Manipulated, edited, or fake.
Matches the visible signature with expected frequency and evolution patterns.
LED Pattern Verification
Confirms the infrared timing sequence captured in-frame.
IR Pulse Check
Verifies that the signature was mathematically signed by that device’s private key.
Cryptographic Validation
Matches the signature to a known registered device.
Device ID Lookup
Checks sensor logs (IMU, gyro, magnetometer, temperature, pressure) against the video’s timeline.
Environmental Log Comparison
If a video claims your device ID, the system:
Runs full internal validation instantly.
- LED + IR + crypto signature checks
- Device log comparison
- Timestamp correlation
Contacts the registered device owner.
- Confirms whether this moment actually occurred
Flags the clip if any mismatch occurs.
Dual-verification system prevents impersonation attacks
Suspicious Clip Handling
Hardware wins because:
Software can be fooled.
AI can imitate voices and faces.
Visual artifacts can be removed or recreated.
But AI cannot forge cryptographic hardware signals matched to real device logs.